Sometimes, it's just not enough to simply know that there's a Trojan or Virus onboard. Sometimes you need to know exactly why that file is onboard, how it got there - but most importantly, who put it there.
By enumerating the attacker in the same way that they have enumerated the victim, you will be able to see the bigger picture and establish what you're up against. But how can you do this? Read on...
## Connections make the world go round ##
The computer world, at any rate. Every single time you open up a website, send an email or upload your webpages into cyberspace, you are connecting to another machine in order to get the job done. This, of course, presents a major problem, because this simple act is what allows malicious users to target a machine in the first place.
# How do these people find their victim?
Well, first of all, they need to get hold of the victim's IP Address. Your IP (Internet Protocol) address reveals your point of entry to the Internet and can be used in many ways to cause your online activities many, many problems. It may not reveal you by name, but it may be uniquely identifiable and it represents your digital ID while you are online (especially so if you're on a fixed IP / DSL etc).
With an IP address, a Hacker can find out all sorts of weird and wonderful things about their victim (as well as causing all kinds of other trouble, the biggest two being Portnukes/Trojans and the dreaded DoS ((Denial of Service)) attack). Some Hackers like to collect IP Addresses like badges, and like to go back to old targets, messing them around every so often. An IP address is incredibly easy to obtain - until recently, many realtime chat applications (such as MSN) were goldmines of information. Your IP Address is contained as part of the Header Code on all emails that you send and webpages that you visit can store all kinds of information about you. A common trick is for the Hacker to go into a Chatroom, paste his supposed website address all over the place, and when the unsuspecting victim visits, everything about your computer from the operating system to the screen resolution can be logged...and, of course, the all important IP address. In addition, a simple network-wide port scan will reveal vulnerable target machines, and a war-dialler will scan thousands of lines for exposed modems that the hacker can exploit.
So now that you know some of the basic dangers, you're probably wondering how these people connect to a victim's machine?
## Virtual and Physical Ports ##
Everything that you recieve over the Internet comes as a result of other machines connecting to your computer's ports. You have two types; Physical are the holes in the back of your machine, but the important ones are Virtual. These allow transfer of data between your computer and the outside world, some with allocated functions, some without, but knowing how these work is the first step to discovering who is attacking you; you simply MUST have a basic knowledge of this, or you won't get much further.
# What the phrases TCP/UDP actually mean
TCP/IP stands for Transmission Control Protocol and Internet Protocol, a TCP/IP packet is a block of data which is compressed, then a header is put on it and it is sent to another computer (UDP stands for User Datagram Protocol). This is how ALL internet transfers occur, by sending packets. The header in a packet contains the IP address of the one who originally sent you it. Now, your computer comes with an excellent (and free) tool that allows you to see anything that is connected (or is attempting to connect) to you, although bear in mind that it offers no blocking protection; it simply tells you what is going on, and that tool is NETSTAT.
## Netstat: Your first line of defence ##
Netstat is a very fast and reliable method of seeing exactly who or what is connected (or connecting) to your computer. Open up DOS (Start/Programs/MS-DOS Prompt on most systems), and in the MSDOS Prompt, type:
netstat -a
(make sure you include the space inbetween the "t" and the "a").
If you're connected to the Internet when you do this, you should see something like:
Quote:
Active Connections
Proto Local Address Foreign Address State
TCP macintosh: 20034 modem-123.tun.dialup.co.uk: 50505 ESTABLISHED
TCP macintosh: 80 proxy.webcache.eng.sq: 30101 TIME_WAIT
TCP macintosh MACINTOSH: 0 LISTENING
TCP macintosh MACINTOSH: 0 LISTENING
TCP macintosh MACINTOSH: 0 LISTENING
Now, "Proto(col)" simply means what kind of data transmission is taking place (TCP or UDP), "Local address" is your computer (and the number next to it tells you what port you're connected on), "Foreign Address" is the machine that is connected to you (and what port they're using), and finally "State" is simply whether or not a connection is actually established, or whether the machine in question is waiting for a transmission, or timing out etc.
Now, you need to know all of Netstat's various commands, so type:
netstat ?
You will get something like this:
Displays protocol statistics and current TCP/IP network connections.
NETSTAT [-a] [-e] [-n] [-s] [-p proto] [-r] [interval]
-a Displays all connections and listening ports.
-e Displays Ethernet statistics. This may be combined with the -s option.
-n Displays addresses and port numbers in numerical form.
-p proto Shows connections for the protocol specified by proto; proto may be TCP or UDP. If used with the -s option to display per-protocol statistics, proto may be TCP, UDP, or IP.
-r Displays the routing table.
-s Displays per-protocol statistics. By default, statistics are shown for TCP, UDP and IP; the -p option may be used to specify a subset of the default.
Have a play around with the various options, but the most important use of these methods is when you combine them. The best command to use is
netstat -an
because this will list all connections in Numerical Form, which makes it a lot easier to trace malicious users....Hostnames can be a little confusing if you don't know what you're doing (although they're easily understandable, as we shall see later). Also, by doing this, you can also find out what your own IP address is, which is always useful.
Also,
netstat -b
will tell you what ports are open and what programs are connecting to the internet.
## Types of Port ##
It would be impossible to find out who was attacking you if computers could just access any old port to perform an important function; how could you tell a mail transfer from a Trojan Attack? Well, good news, because your regular, normal connections are assigned to low, commonly used ports, and in general, the higher the number used, the more you should be suspicious. Here are the three main types of port:
# Well Known PortsThese run from 0 to 1023, and are bound to the common services that run on them (for example, mail runs on channel 25 tcp/udp, which is smtp (Simple Mail Transfer Protocol) so if you find one of these ports open (and you usually will), it's usually because of an essential function.
# Registered PortsThese run on 1024 to 49151. Although not bound to a particular service, these are normally used by networking utilities like FTP software, Email client and so on, and they do this by opening on a random port within this range before communicating with the remote server, so don't panic (just be wary, perhaps) if you see any of these open, because they usually close automatically when the system that's running on them terminates (for example, type in a common website name in your browser with netstat open, and watch as it opens up a port at random to act as a buffer for the remote servers). Services like MSN Messenger and ICQ usually run on these Ports.
# Dynamic/Private PortsRanging from 49152 to 65535, these things are rarely used except with certain programs, and even then not very often. This is indeed the usual range of the Trojan, so if you find any of these open, be very suspicious. So, just to recap:
Quote:
Well Known Ports 0 to 1023 Commonly used, little danger.
Registered Ports 1024 to 49151 Not as common, just be careful.
Dynamic/Private Ports 49152 to 65535 Be extremely suspicious.
## The hunt is on ##
Now, it is essential that you know what you're looking for, and the most common way someone will attack your machine is with a Trojan. This is a program that is sent to you in an email, or attempts to bind itself to one of your ports, and when activated, it can give the user your passwords, access to your hard drive...they can even make your CD Tray pop open and shut. At the end of this Document, you will find a list of the most commonly used Trojans and the ports they operate on. For now, let's take another look at that first example of Netstat....
Quote:
Active Connections
Proto Local Address Foreign Address State
TCP macintosh: 27374 modem-123.tun.dialup.co.uk: 50505 ESTABLISHED
TCP macintosh: 80 proxy.webcache.eng.sq: 30101 TIME_WAIT
TCP macintosh MACINTOSH: 0 LISTENING
TCP macintosh MACINTOSH: 0 LISTENING
TCP macintosh MACINTOSH: 0 LISTENING
Now, straight away, this should make more sense to you. Your computer is connected on two ports, 80 and 27374. Port 80 is used for http/www transmissions (ie for all intents and purposes, its how you connect to the net, although of course it's a lot more complicated than that). Port 27374, however, is distinctly suspicious; first of all, it is in the registered port range, and although other services (like MSN) use these, let's assume that you have nothing at all running like instant messengers, webpages etc....you're simply connected to the net through proxy. So, now this connection is looking even more troublesome, and when you realise that 27374 is a common port for Netbus (a potentially destructive Trojan), you can see that something is untoward here. So, what you would do is:
Quote:
1) run Netstat , and use:
Netstat -a
then
Netstat -an
So you have both Hostnames AND IP addresses.
Tracerouting ##
Having the attacker's IP is all well and good, but what can you do with it? The answer is, a lot more! It's not enough to have the address, you also need to know where the attacker's connections are coming from. You may have used automated tracerouting tools before, but do you jknow how they work?
Go back to MSDOS and type
Quote:
tracert *type IP address/Hostname here*
Now, what happens is, the Traceroute will show you all the computers inbetween you and the target machine, including blockages, firewalls etc. More often than not, the hostname address listed before the final one will belong to the Hacker's ISP Company. It'll either say who the ISP is somewhere in there, or else you run a second trace on the new IP/hostname address to see who the ISP Company in question is. If the Hostname that you get back doesn't actually seem to mention an actual geographical location within its text, you may think all is lost. But fear not! Suppose you get a hostname such as http://www.haha.com
Well, that tells us nothing, right? Wrong....simply enter the hostname in your browser, and though many times you will get nothing back, sometimes it will resolve to an ISP, and from there you can easily find out its location and in what areas they operate. This at least gives you a firm geographical location to carry out your investigations in.
If you STILL have nothing, as a last resort you COULD try connecting to your target's ISP's port 13 by Telnet, which will tell you how many hours ahead or behind this ISP is of GMT, thus giving you a geographical trace based on the time mentioned (although bear in mind, the ISP may be doing something stupid like not having their clocks set correctly, giving you a misleading trace. Similarly, a common tactic of Hackers is to deliberately have their computer's clock set to a totally wrong time, so as to throw you off the scent). Also, unless you know what you're doing, I wouldn't advise using Telnet (which is outside the parameters of this tutorial).
## Reverse DNS Query ##
This is probably the most effective way of running a trace on somebody. If ever you're in a chatroom and you see someone saying that they've "hacked into a satellite orbiting the Earth, and are taking pictures of your house right now", ignore them because that's just bad movie nonsense. THIS method is the way to go, with regard to finding out what country (even maybe what State/City etc) someone resides, although it's actually almost impossible to find an EXACT geographical location without actually breaking into your ISP's Head Office and running off with the safe.
To run an rDNS query, simply go back to MS-DOS and type
netstat
and hit return. Any active connections will resolve to hostnames rather than a numerical format.
# DNS
DNS stands for Domain Name Server. These are machines connected to the Internet whose job it is to keep track of the IP Addresses and Domain Names of other machines. When called upon, they take the ASCII Domain Name and convert it to the relevant numeric IP Address. A DNS search translates a hostname into an IP address....which is why we can enter "www.Hotmail.com" and get the website to come up, instead of having to actually remember Hotmail's IP address and enter that instead. Well, Reverse DNS, of course, translates the IP Address into a Hostname (ie - in letters and words instead of numbers, because sometimes the Hacker will employ various methods to stop Netstat from picking up a correct Hostname).
So, for example,
298.12.87.32 is NOT a Hostname.
mail6.bol.net.au IS a Hostname.
Anyway, see the section at the end? (au) means the target lives in Australia. Most (if not all) hostnames end in a specific Country Code, thus narrowing down your search even further. If you know your target's Email Address (ie they foolishly sent you a hate mail, but were silly enough to use a valid email address) but nothing else, then you can use the Country codes to deduce where they're from as well. You can also deduce the IP address of the sender by looking at the emails header (a "hidden" line of code which contains information on the sender)...on Hotmail for example, go to Preferences, and select the "Full Header's Visible" option. Alternatively, you can run a "Finger" Trace on the email address, at: http://www.samspade.org
Plus, some ISP's include their name in your Email Address with them too (ie Wanadoo, Supanet etc), and your Hacker may be using an email account that's been provided by a Website hosting company, meaning this would probably have the website host's name in the email address (ie Webspawners). So, you could use the information gleaned to maybe even hunt down their website (then you could run a website check as mentioned previously) or report abuse of that Website Provider's Email account (and thus, the Website that it goes with) to abuse@companynamegoeshere.com
If your Hacker happens to reside in the USA, go to: http://www.usps.gov/ncsc/lookups/abbr_state.txt
for a complete list of US State abbreviatons.
## List of Ports commonly used by Trojans ##
Please note that this isn't a complete list by any means, but it will give you an idea of what to look out for in Netstat. Be aware that some of the lower Ports may well be running valid services.
UDP: 1349 Back Ofrice DLL
31337 BackOfrice 1.20
31338 DeepBO
54321 BackOfrice 2000
TCP: 21 Blade Runner, Doly Trojan, Fore, Invisible FTP, WebEx, WinCrash
23 Tiny Telnet Server
25 Antigen, Email Password Sender, Haebu Coceda, Shtrilitz Stealth, Terminator, WinPC, WinSpy, Kuang2 0.17A-0.30
31 Hackers Paradise
80 Executor
456 Hackers Paradise
555 Ini-Killer, Phase Zero, Stealth Spy
666 Satanz Backdoor
1001 Silencer, WebEx
1011 Doly Trojan
1170 Psyber Stream Server, Voice
1234 Ultors Trojan
1243 SubSeven 1.0 - 1.8
1245 VooDoo Doll
1492 FTP99CMP
1600 Shivka-Burka
1807 SpySender
1981 Shockrave
1999 BackDoor 1.00-1.03
2001 Trojan Cow
2023 Ripper
2115 Bugs
2140 Deep Throat, The Invasor
2801 Phineas Phucker
3024 WinCrash
3129 Masters Paradise
3150 Deep Throat, The Invasor
3700 Portal of Doom
4092 WinCrash
4567 File Nail 1
4590 ICQTrojan
5000 Bubbel
5000 Sockets de Troie
5001 Sockets de Troie
5321 Firehotcker
5400 Blade Runner 0.80 Alpha
5401 Blade Runner 0.80 Alpha
5402 Blade Runner 0.80 Alpha
5400 Blade Runner
5401 Blade Runner
5402 Blade Runner
5569 Robo-Hack
5742 WinCrash
6670 DeepThroat
6771 DeepThroat
6969 GateCrasher, Priority
7000 Remote Grab
7300 NetMonitor
7301 NetMonitor
7306 NetMonitor
7307 NetMonitor
7308 NetMonitor
7789 ICKiller
8787 BackOfrice 2000
9872 Portal of Doom
9873 Portal of Doom
9874 Portal of Doom
9875 Portal of Doom
9989 iNi-Killer
10067 Portal of Doom
10167 Portal of Doom
10607 Coma 1.0.9
11000 Senna Spy
11223 Progenic trojan
12223 Hack´99 KeyLogger
12345 GabanBus, NetBus
12346 GabanBus, NetBus
12361 Whack-a-mole
12362 Whack-a-mole
16969 Priority
20001 Millennium
20034 NetBus 2.0, Beta-NetBus 2.01
21544 GirlFriend 1.0, Beta-1.35
22222 Prosiak
23456 Evil FTP, Ugly FTP
26274 Delta
30100 NetSphere 1.27a
30101 NetSphere 1.27a
30102 NetSphere 1.27a
31337 Back Orifice
31338 Back Orifice, DeepBO
31339 NetSpy DK
31666 BOWhack
33333 Prosiak
34324 BigGluck, TN
40412 The Spy
40421 Masters Paradise
40422 Masters Paradise
40423 Masters Paradise
40426 Masters Paradise
47262 Delta
50505 Sockets de Troie
50766 Fore
53001 Remote Windows Shutdown
54321 SchoolBus .69-1.11
61466 Telecommando
65000 Devil
## Summary ##
I hope this tutorial is useful in showing you both how to secure yourself against unwanted connections, and also how to determine an attacker's identity. The Internet is by no means as anonymous as some people think it is, and although this is to the detriment of people's security online, this also works both ways....it IS possible to find and stop even the most determined of attackers, you just have to be patient and keep hunting for clues which will help you put an end to their exploits.
by hy2r0gen
Well in the unlikely case that they do actually decide to track you here are a few rules you should live by.
Some of these are really more directed at new-comers to the scene since most experienced hackers learn these by trial and error.
::Always use a proxy::
Pretty simple, this is your no.1 defense against getting tracked down since your IP is like a fingerprint. If they have an IP they have an ISP, if they have a warrant they have name, number, address, credit card number and everything that you have given your ISP. Proxys and VPNs are a hackers best friend...so get to know how to use them and never forgot them.
::Never enter personal details::
When you are doing ANYTHING illegal never link to, or enter personal information. This is from your name to when you got your first gf. If they don't know who you are...then who are they gonna charge.
::Never Admit Wrong Doing::
Every business you will ever work in will tell you, when the customer complains...sympathize but never admit that its the businesses fault.
If you are ever contacted by a police force from anywhere in the world saying they want accounts back etc. (even if you think its spoofed) NEVER be a smart ass and say "PWND YOU ***, IM 12 WTF YOU GONA DO **********
Think about it, if they have enough evidence (unlikely as it sounds) they may extradite you. I wish I was joking but Governments all over the world are taking a stance on cyber crime. And making an example of a teenager is a small price to pay if it deters 1,000's of teenagers.
They are doing a similar thing in the piracy department, some guy got busted with like 10 burnt DVD's and was charged and orded to pay in excess of $50,000 just to make an example of him...and it worked, scared the shit outta pirates everywhere.
So why risk it...they may be 100% legit police or law enforcement agency and you have admitted you fucked them over. Not a good look in-front of the magistrate
::Don't be Stupid::
DO NOT HACK .gov, .edu or any other government body. You will get fucked and investigated. So simple stay away from them and save the jail time.
::Don't Brag about things which you may be investigated about::
This falls under the same category of admission. If you hacked a PayPal account and transferred $10,000 without anyone know...KEEP IT TO YOURSELF. A username that you use commonly = a name on a social networking site which = a location, address...everything
"loose lips, sink ships"
::Blame Game::
If you get an email and you feel compelled to respond (i recommend you close the whole account in this circumstance) say you have no idea what they are talking about. Say that someone may have hack your wireless becuase you have been to lazy to put a WEP/WPA on it. Or try and say that you have been in another country/state/neighborhood/visiting grandparents for the last two weeks and someone broke into your house, but nothing was stolen so you didn't report it.
Basically say shit that:
a) doesn't point to you being involved at all
b) leads them to a dead end
This will stall if not stop the whole process, because there isn't much they can do to prove you were the actual person sitting at the keyboard. Thats why its so important to keep personal files away from this aspect of your life and to NEVER admit you did it.
::Worldwide::
Just because I hack a Russian website means that I am safe from getting in trouble. New CyberCrime laws are being much more flexible to cater for such things. So if you think your safe because they are 10,000kms away...think again and follow the above rules.
::Evidence::
Ok, so you've confirmed there is an investigation with possible serious consequences. Any day cops will be at your door...format your HDD 12 times for a clean HD. Better yet throw it in the microwave for 2 mins. Anther good idea submitted by Cruzr,keep an electro magnet either inside or on top your tower. Electro magnets are safe to sit next to objects since the do not become magnetic until a electrical current enters the circuit. So if the Police kick in your door at 3am, switch her on and bam...your cleared of any evidence. But i will point out that if they seize a HD that has been formatted <
REMEMBER HACKING IS A CRIME !!
![[Image: 2po1w5s.jpg]](http://i41.tinypic.com/2po1w5s.jpg)
Brand New Ebook Reveals 21 Proven Income Streams That You Can Use to Make Money Online Anytime You Want!
"21 Income Streams: Multiple Ways to Make Money Online"
Joanne Mason | ISBN: N\A | price $27 but I give you for free | PDF | 5,67 mb
Joanne Mason has written an ebook tittled 21 Income Streams: Multiple Ways To Make Money Online. This ebook shows
21 profit pulling techniques that are a surefire methods seen first hand and can attest to the money making
potential in every single one and its yours for free. Here?s a teaser of whats inside:
- How to Make Money Online with Affiliate Programs
- How to Make Money Online with Blogs
- How to Make Money Online with eBooks
- How to Make Money Online with ebay Referrals
- How to Make Money Online with Your Own Niche Directory
- How to Make Money Online with an Internet Radio Show
- How to Make Money Online Selling Stock Photos
- How to Make Money Online Interviewing Experts
- How to Make Money Online with a Classified Advertising Site
- How to Make Money Online with a Local Real Estate Portal
- How to Make Money Online Creating Your Own Software
- How to Make Money Online with Teleseminars & Webinars
- How to Make Money Online with Residual Income Programs
- How to Make Money Online with Audio eCourses
- How to Make Money Online as a Coach/Consultant
- How to Make Money Online with a Content Site
- How to Make Money Online as a Virtual Assistant
- How to Make Money Online a Local Online Mall
- How to Make Money Online with a Social Networking Site
- How to Make Money Online Providing Helpdesk Support
- How to Make Money Online with Your Own Membership Site
Very informative information for newbies and advanced internet marketers.
http://hotfile.com/dl/9297596/2095503/Make_money.rar.html
THE ART OF DECEPTION
Controlling the Human Element of Security
KEVIN D. MITNICK
& William L. Simon
Foreword by Steve Wozniak
For Reba Vartanian, Shelly Jaffe, Chickie Leventhal, and Mitchell
Mitnick, and for the late Alan Mitnick, Adam Mitnick, and Jack Biello
For Arynne, Victoria, and David, Sheldon,Vincent, and Elena.
Social Engineering
Social Engineering uses influence and persuasion to deceive people
by convincing them that the social engineer is someone he is not,
or by manipulation. As a result, the social engineer is able to take
advantage of people to obtain information with or without the use of
technology.
http://rapidshare.com/files/65452273/The_Art_of_Deception_by_Kevin_D._Mitnick.pdf
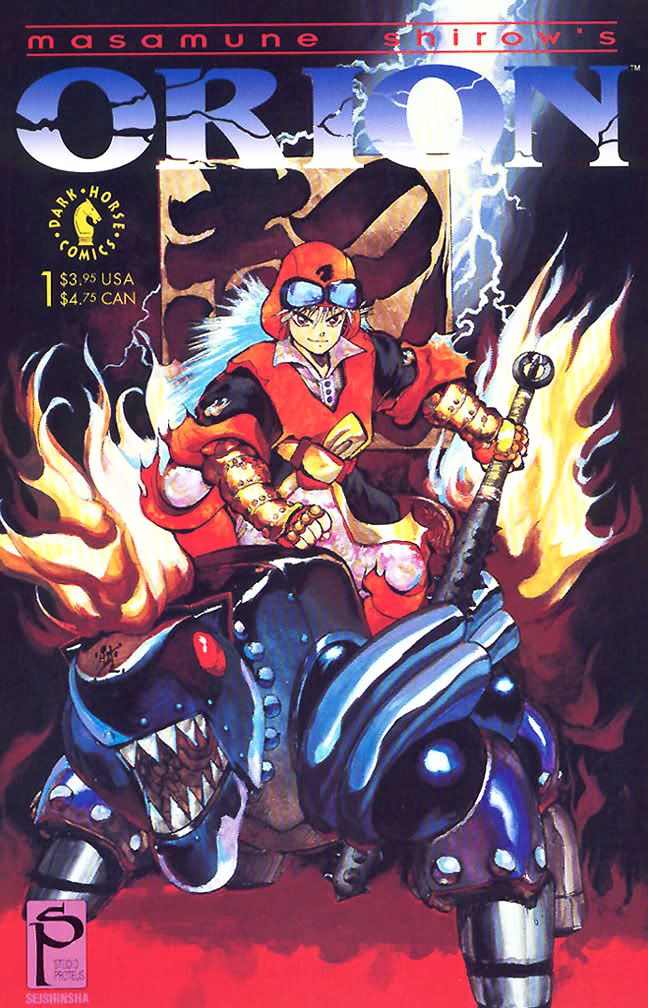
Orion manga [by masamune shirow]
Scans were by the MangaProject scanslation group founders ZlleH and Ichijo in 2001 onwards. Issues were released in comic book format. Color scans are available for the front and back covers and range in size from 650 x 1010 to a HQ version of approx 1185 x 1820. Interior manga pages are BW and range in size from 650 x 1010 to a larger 865 x 1370. The scans are clean and well-centered (not skewed). Language: English Size: 61318 KB «»«»«»«»«» ORION OVERVIEW «»«»«»«»«»
Title: Orion
Story and art by Masamune Shirow (Appleseed, Black Magic, Dominion, Ghost in the Shell, Intron Depot)
Date: 1988 (original creation)
Main Characters: Dr. Gyoun Hebime, Susano Orbatos, Master Fuzen, Princess Kushinata, Seska Fuzen
From the Published Book Synopsis:
In the mighty Yamata Empire, magic and technology are one and the same. Now the Empire is preparing its ultimate feat of psycho-science: the destruction of all the negative karma in the galaxy. But will this mystical purification be the salvation of humanity -- or its ultimate destruction? Only one being can save the Empire from its folly: Susano, the God of Destruction.Wild, arrogant, and homicidal, Susano has come to teach the world the true nature of power!
Shirow's Comments on Orion from Intron Depot:
Orion is a light-hearted manga; sort of a comedy based on Japanese mythology, seasoned with H.P. Lovecraft's Cthulhu mythos. It's the story of Earth's genesis (destruction?), triggered by sorcerers in super-ancient times who summon gods and use special nine-headed Naga rituals (this is obviously fiction, and I beg forgiveness of any Christian or Hindu readers- all religions have their own creation myths, after all). I may have gone overboard a bit with all the kanji double and triple meanings that I used, but its a rather conceptual story, and I had a lot of fun drawing it. Perhaps as a result, Orion also has a slightly raw rhythm to it. Interestingly, the target readership turned out to be quite a bit different in the end than I had originally planned. I think of Orion as being in the same vein as Black Magic, and sort of a counterpart to Appleseed. Personal Note from S0rath: This is one of those golden oldies manga by Masamune Shirow that featured cyberpunk and sci-fi. This is one for those hardcore collectors and also for the very new with manga.
http://rapidshare.com/files/272935921/Masamune_Shirow_-_Orion.rar
![[Image: 4.jpg]](http://reversengineering.files.wordpress.com/2008/05/4.jpg)
